The Latest
-
Salesloft OAuth Breach via Drift AI Chat Agent Exposes Salesforce Customer Data
-
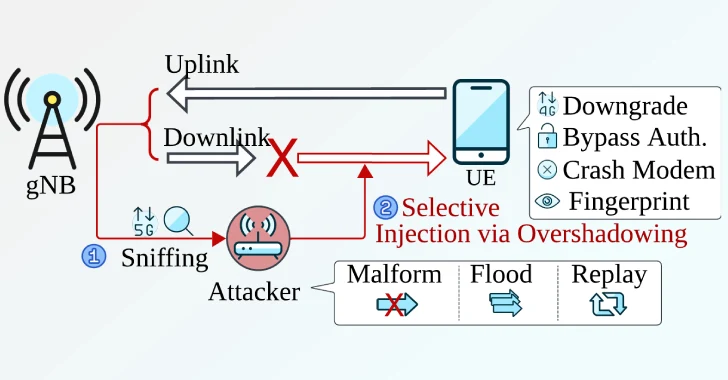
New Sni5Gect Attack Crashes Phones and Downgrades 5G to 4G without Rogue Base Station
-
Citrix Patches Three NetScaler Flaws, Confirms Active Exploitation of CVE-2025-7775
-
MixShell Malware Delivered via Contact Forms Targets U.S. Supply Chain Manufacturers