The Latest
-
Chaos RaaS Emerges After BlackSuit Takedown, Demanding $300K from U.S. Victims
-
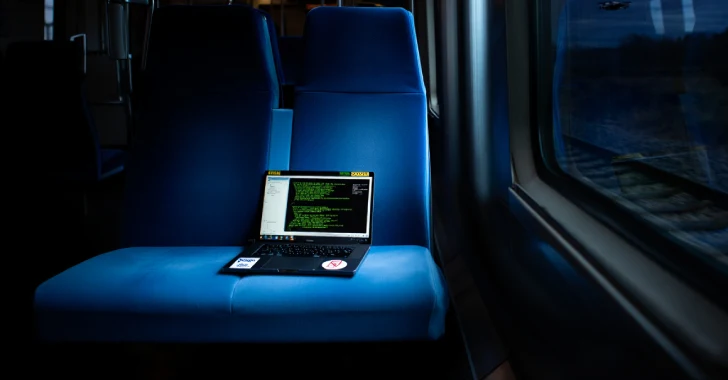
Why React Didn't Kill XSS: The New JavaScript Injection Playbook
-
Cybercriminals Use Fake Apps to Steal Data and Blackmail Users Across Asia’s Mobile Networks
-
How the Browser Became the Main Cyber Battleground