The Latest
-
CBI Shuts Down £390K U.K. Tech Support Scam, Arrests Key Operatives in Noida Call Center
-
eSIM Vulnerability in Kigen's eUICC Cards Exposes Billions of IoT Devices to Malicious Attacks
-
GPUHammer: New RowHammer Attack Variant Degrades AI Models on NVIDIA GPUs
-
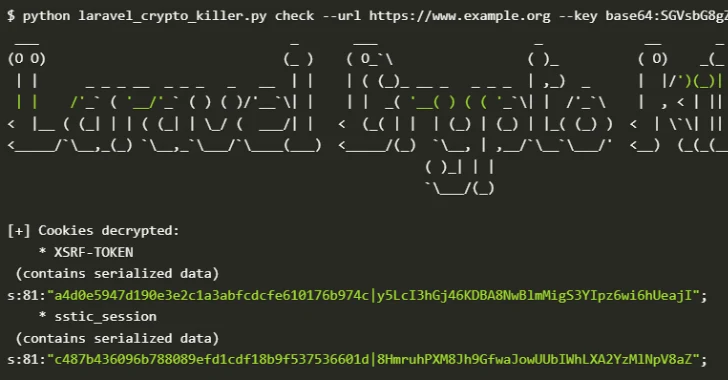
Over 600 Laravel Apps Exposed to Remote Code Execution Due to Leaked APP_KEYs on GitHub