The Latest
-
Webinar: Learn How to Unite Dev, Sec, and Ops Teams With One Shared Playbook
-
Abandoned Sogou Zhuyin Update Server Hijacked, Weaponized in Taiwan Espionage Campaign
-
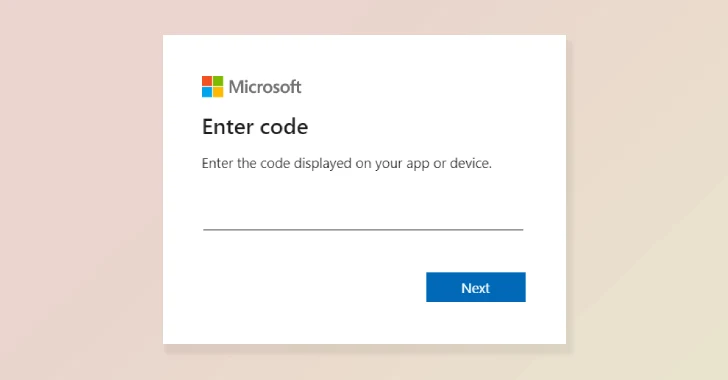
Amazon Disrupts APT29 Watering Hole Campaign Abusing Microsoft Device Code Authentication
-
Salt Typhoon Exploits Flaws in Edge Network Devices to Breach 600 Organizations Worldwide