The Latest
-
The Wild West of Shadow IT
-
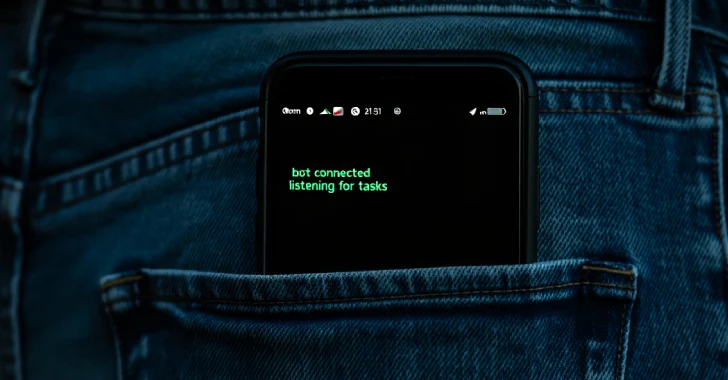
PlayPraetor Android Trojan Infects 11,000+ Devices via Fake Google Play Pages and Meta Ads
-
CL-STA-0969 Installs Covert Malware in Telecom Networks During 10-Month Espionage Campaign
-
New ‘Plague’ PAM Backdoor Exposes Critical Linux Systems to Silent Credential Theft