The Latest
-
Smishing Triad Linked to 194,000 Malicious Domains in Global Phishing Operation
-
'Jingle Thief' Hackers Exploit Cloud Infrastructure to Steal Millions in Gift Cards
-
Microsoft Issues Emergency Patch for Actively Exploited Critical WSUS Vulnerability
-
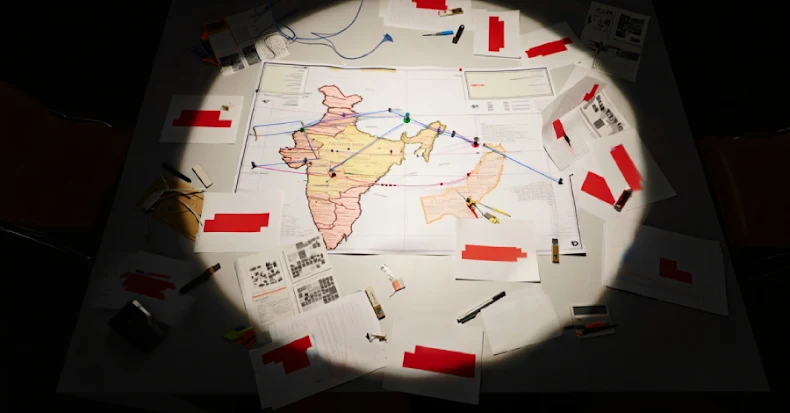
APT36 Targets Indian Government with Golang-Based DeskRAT Malware Campaign