The Latest
-
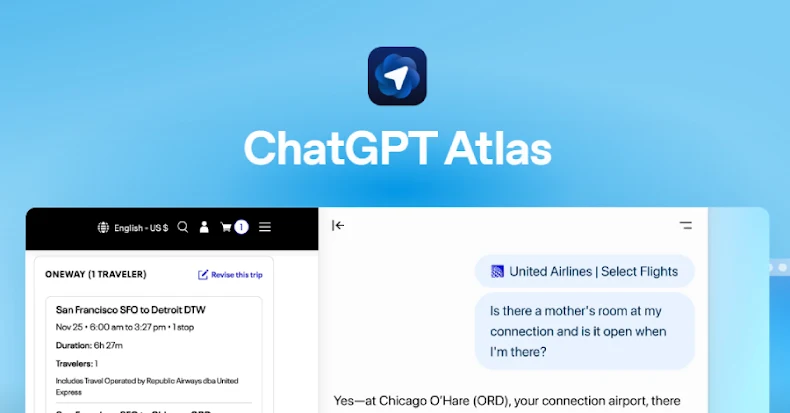
ChatGPT Atlas Browser Can Be Tricked by Fake URLs into Executing Hidden Commands
-
Newly Patched Critical Microsoft WSUS Flaw Comes Under Active Exploitation
-
Smishing Triad Linked to 194,000 Malicious Domains in Global Phishing Operation
-
'Jingle Thief' Hackers Exploit Cloud Infrastructure to Steal Millions in Gift Cards