The Latest
-
State-Sponsored Hackers Exploiting Libraesva Email Security Gateway Vulnerability
-
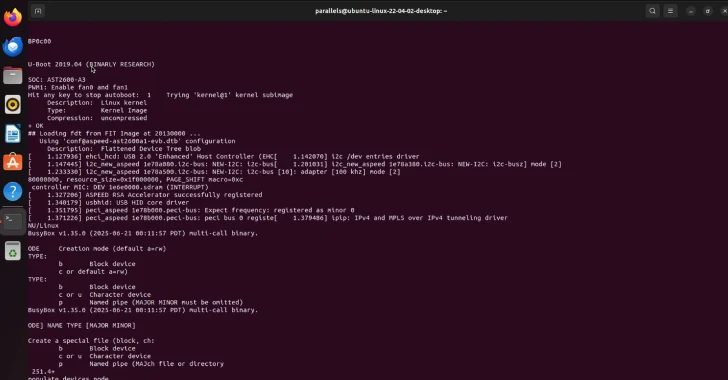
Two New Supermicro BMC Bugs Allow Malicious Firmware to Evade Root of Trust Security
-
Eurojust Arrests 5 in €100M Cryptocurrency Investment Fraud Spanning 23 Countries
-
U.S. Secret Service Seizes 300 SIM Servers, 100K Cards Threatening U.S. Officials Near UN