The Latest
-
How to Gain Control of AI Agents and Non-Human Identities
-
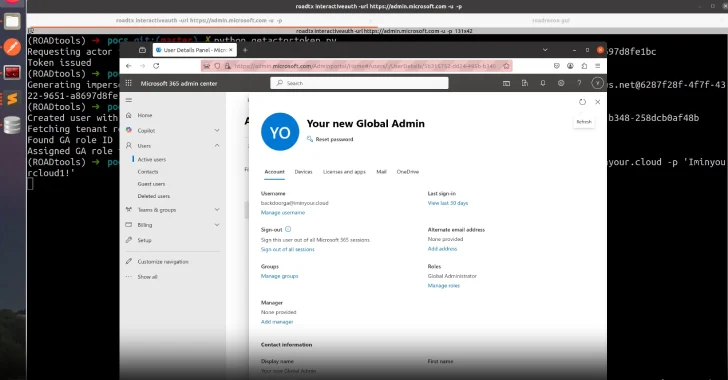
Microsoft Patches Critical Entra ID Flaw Enabling Global Admin Impersonation Across Tenants
-
DPRK Hackers Use ClickFix to Deliver BeaverTail Malware in Crypto Job Scams
-
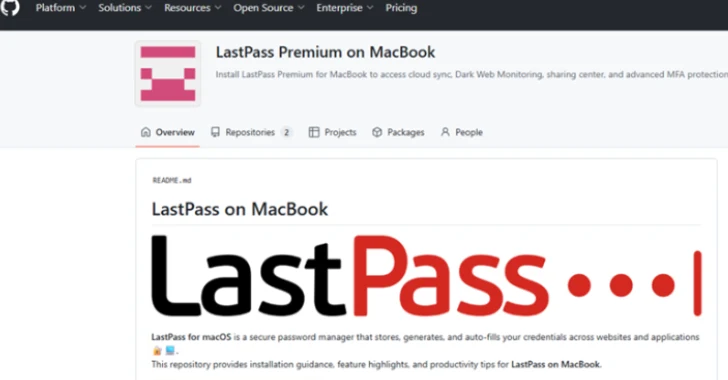
LastPass Warns of Fake Repositories Infecting macOS with Atomic Infostealer