The Latest
-
Sneaky 2FA Phishing Kit Adds BitB Pop-ups Designed to Mimic the Browser Address Bar
-
Meta Expands WhatsApp Security Research with New Proxy Tool and $4M in Bounties This Year
-
Iranian Hackers Use DEEPROOT and TWOSTROKE Malware in Aerospace and Defense Attacks
-
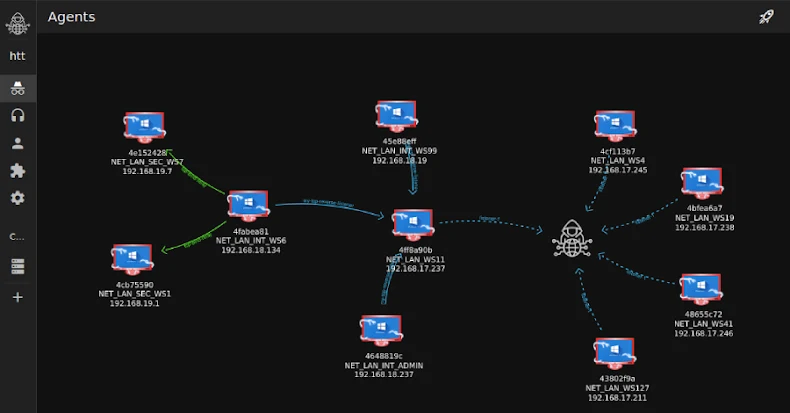
Researchers Detail Tuoni C2's Role in an Attempted 2025 Real-Estate Cyber Intrusion