The Latest
-
Critical Dahua Camera Flaws Enable Remote Hijack via ONVIF and File Upload Exploits
-
Apple Patches Safari Vulnerability Also Exploited as Zero-Day in Google Chrome
-
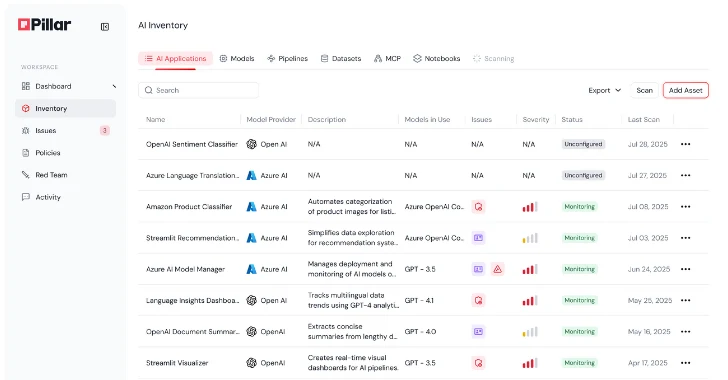
Product Walkthrough: A Look Inside Pillar's AI Security Platform
-
Chinese Firms Linked to Silk Typhoon Filed 15+ Patents for Cyber Espionage Tools