The Latest
-
Hackers Exploit SharePoint Zero-Day Since July 7 to Steal Keys, Maintain Persistent Access
-
China-Linked Hackers Launch Targeted Espionage Campaign on African IT Infrastructure
-
Iran-Linked DCHSpy Android Malware Masquerades as VPN Apps to Spy on Dissidents
-
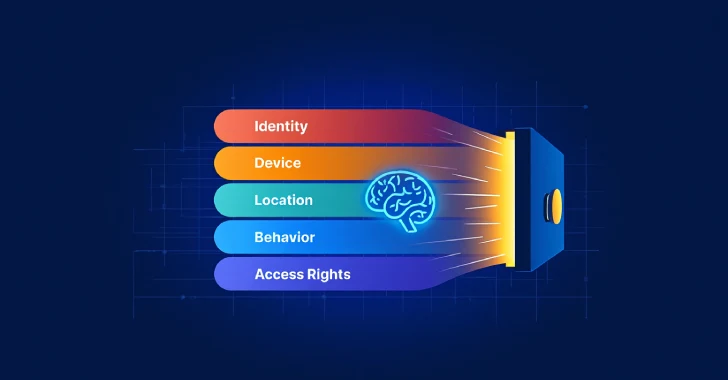
Assessing the Role of AI in Zero Trust