The Latest
-
U.S. Sanctions Garantex and Grinex Over $100M in Ransomware-Linked Illicit Crypto Transactions
-
Cisco Warns of CVSS 10.0 FMC RADIUS Flaw Allowing Remote Code Execution
-
New HTTP/2 'MadeYouReset' Vulnerability Enables Large-Scale DoS Attacks
-
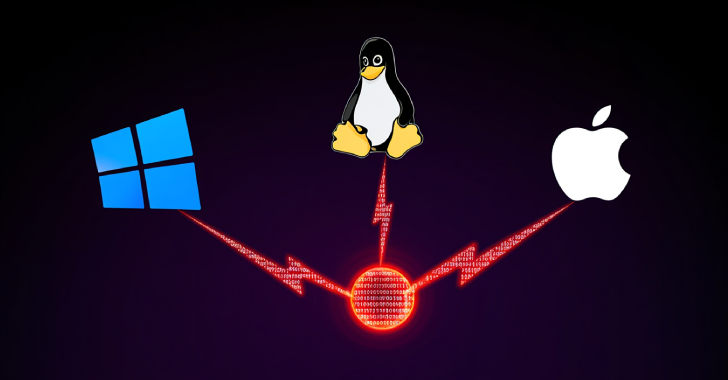
Hackers Found Using CrossC2 to Expand Cobalt Strike Beacon’s Reach to Linux and macOS