The Latest
-
U.K. Government Drops Apple Encryption Backdoor Order After U.S. Civil Liberties Pushback
-
PyPI Blocks 1,800 Expired-Domain Emails to Prevent Account Takeovers and Supply Chain Attacks
-
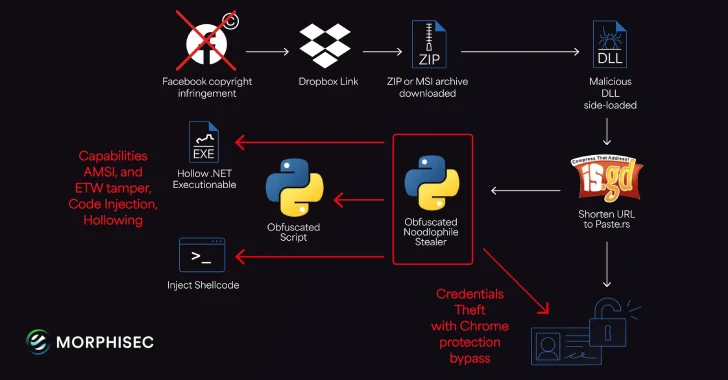
Noodlophile Malware Campaign Expands Global Reach with Copyright Phishing Lures
-
Microsoft Windows Vulnerability Exploited to Deploy PipeMagic RansomExx Malware