The Latest
-
GlassWorm Malware Discovered in Three VS Code Extensions with Thousands of Installs
-
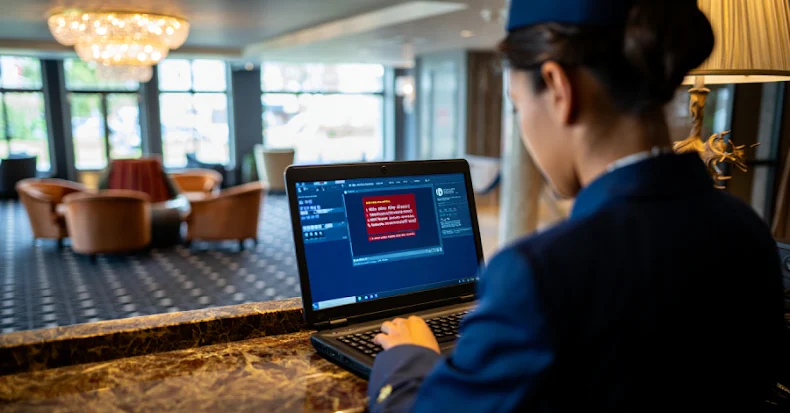
Large-Scale ClickFix Phishing Attacks Target Hotel Systems with PureRAT Malware
-
Microsoft Uncovers 'Whisper Leak' Attack That Identifies AI Chat Topics in Encrypted Traffic
-
Samsung Mobile Flaw Exploited as Zero-Day to Deploy LANDFALL Android Spyware