The Latest
-
CERT-UA Warns of HTA-Delivered C# Malware Attacks Using Court Summons Lures
-
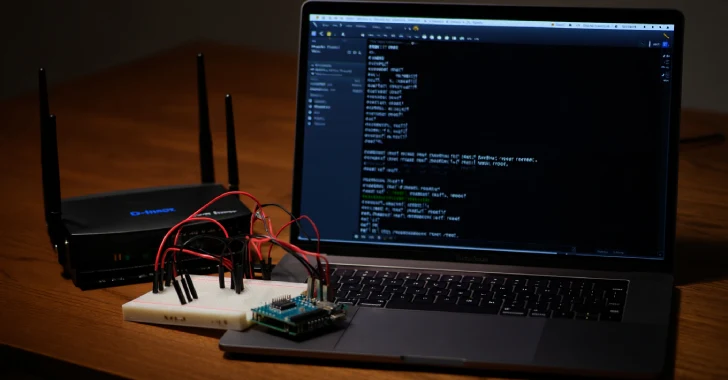
CISA Adds 3 D-Link Vulnerabilities to KEV Catalog Amid Active Exploitation Evidence
-
CISA Adds 3 D-Link Router Flaws to KEV Catalog After Active Exploitation Reports
-
AI Is Transforming Cybersecurity Adversarial Testing – Pentera Founder’s Vision