The Latest
-
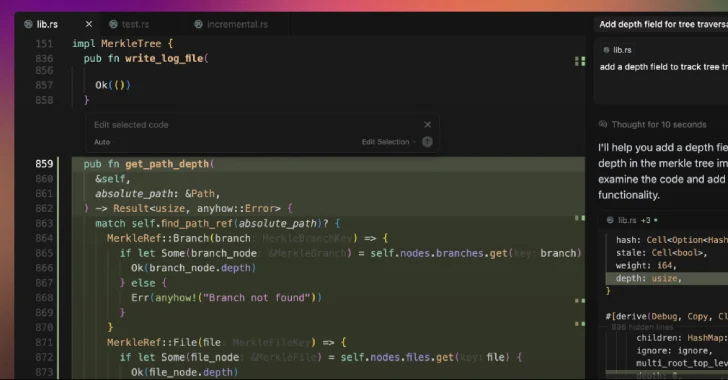
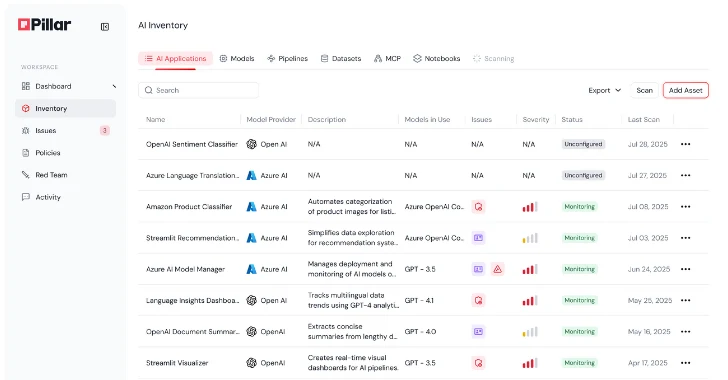
Product Walkthrough: A Look Inside Pillar's AI Security Platform
-
Chinese Firms Linked to Silk Typhoon Filed 15+ Patents for Cyber Espionage Tools
-
Google Launches DBSC Open Beta in Chrome and Enhances Patch Transparency via Project Zero
-
Scattered Spider Hacker Arrests Halt Attacks, But Copycat Threats Sustain Security Pressure