The Latest
-
Malicious PyPI and npm Packages Discovered Exploiting Dependencies in Supply Chain Attacks
-
Wazuh for Regulatory Compliance
-
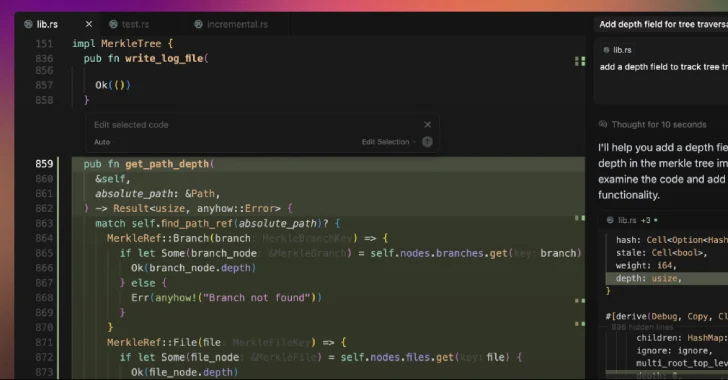
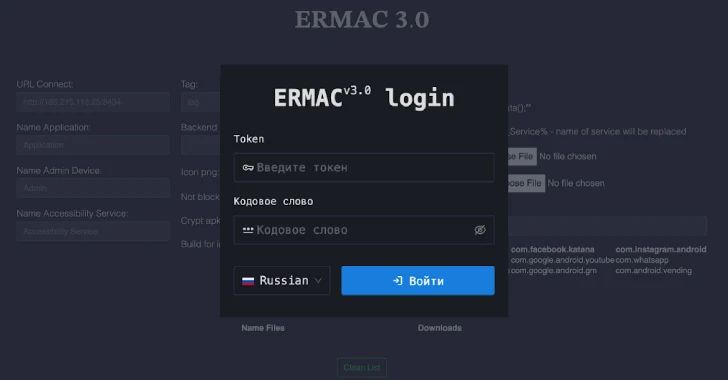
ERMAC V3.0 Banking Trojan Source Code Leak Exposes Full Malware Infrastructure
-
Russian Group EncryptHub Exploits MSC EvilTwin Vulnerability to Deploy Fickle Stealer Malware