The Latest
-
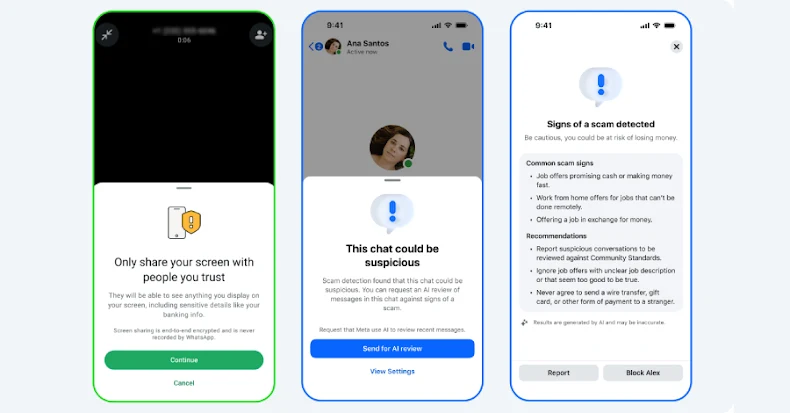
Meta Rolls Out New Tools to Protect WhatsApp and Messenger Users from Scams
-
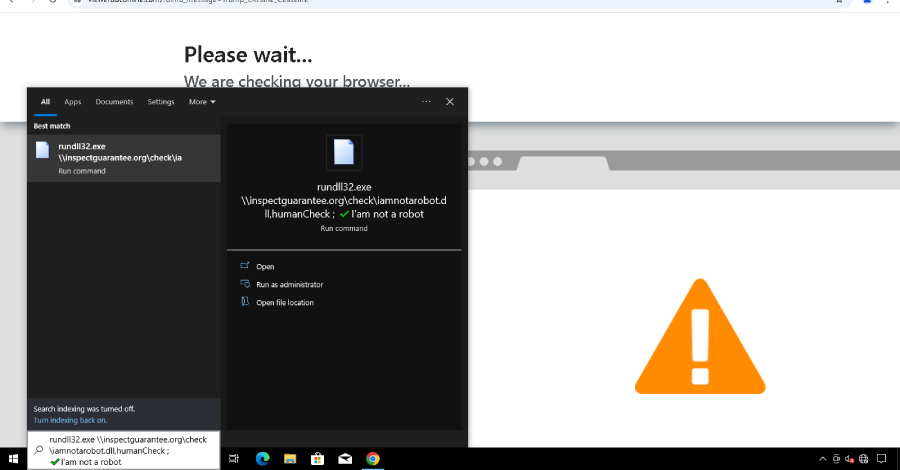
Securing AI to Benefit from AI
-
Hackers Used Snappybee Malware and Citrix Flaw to Breach European Telecom Network
-
Google Identifies Three New Russian Malware Families Created by COLDRIVER Hackers