The Latest
-
From Quantum Hacks to AI Defenses – Expert Guide to Building Unbreakable Cyber Resilience
-
Rethinking AI Data Security: A Buyer's Guide
-
Scattered Spider Resurfaces With Financial Sector Attacks Despite Retirement Claims
-
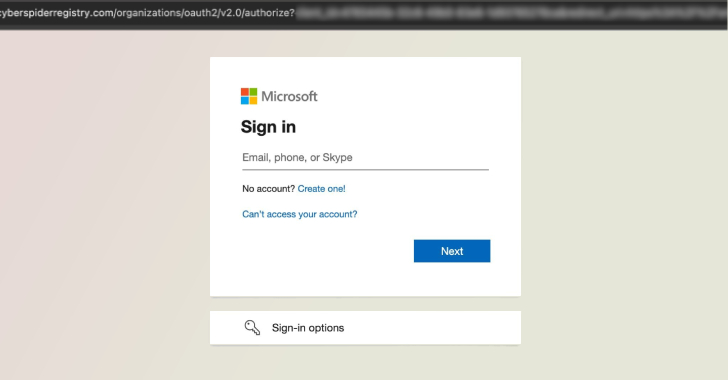
RaccoonO365 Phishing Network Dismantled as Microsoft, Cloudflare Take Down 338 Domains