The Latest
-
Apple Backports Fix for CVE-2025-43300 Exploited in Sophisticated Spyware Attack
-
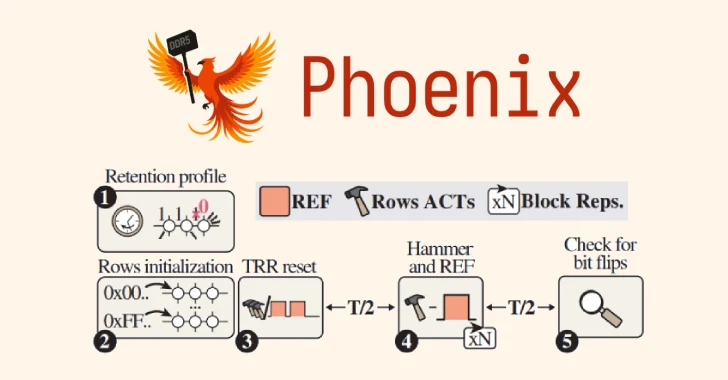
Phoenix RowHammer Attack Bypasses Advanced DDR5 Memory Protections in 109 Seconds
-
40 npm Packages Compromised in Supply Chain Attack Using bundle.js to Steal Credentials
-
Mustang Panda Deploys SnakeDisk USB Worm to Deliver Yokai Backdoor on Thailand IPs