The Latest
-
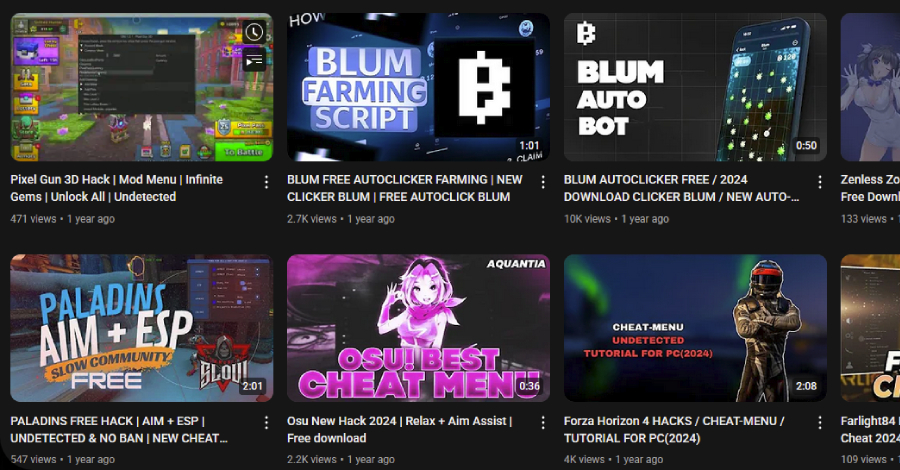
3,000 YouTube Videos Exposed as Malware Traps in Massive Ghost Network Operation
-
Self-Spreading 'GlassWorm' Infects VS Code Extensions in Widespread Supply Chain Attack
-
North Korean Hackers Lure Defense Engineers With Fake Jobs to Steal Drone Secrets
-
ThreatsDay Bulletin: $176M Crypto Fine, Hacking Formula 1, Chromium Vulns, AI Hijack & More