The Latest
-
[Webinar] Shadow AI Agents Multiply Fast — Learn How to Detect and Control Them
-
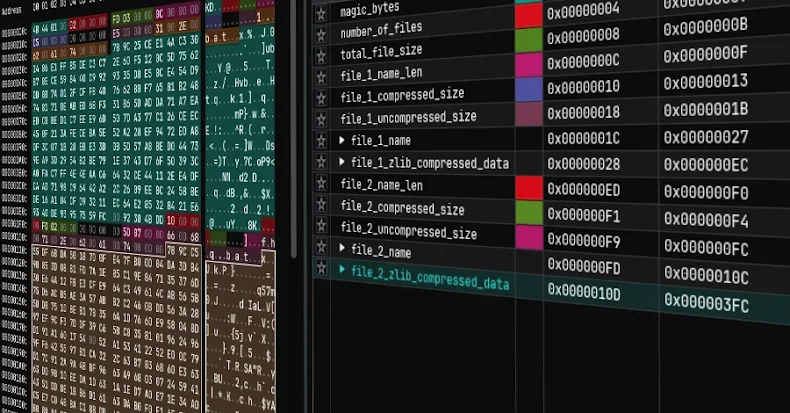
TOR-Based Cryptojacking Attack Expands Through Misconfigured Docker APIs
-
From MostereRAT to ClickFix: New Malware Campaigns Highlight Rising AI and Phishing Risks
-
How Leading CISOs are Getting Budget Approval
![[Webinar] Shadow AI Agents Multiply Fast — Learn How to Detect and Control Them](https://computerodyssey.net/wp-content/uploads/2025/09/wp-header-logo-39.png)