The Latest
-
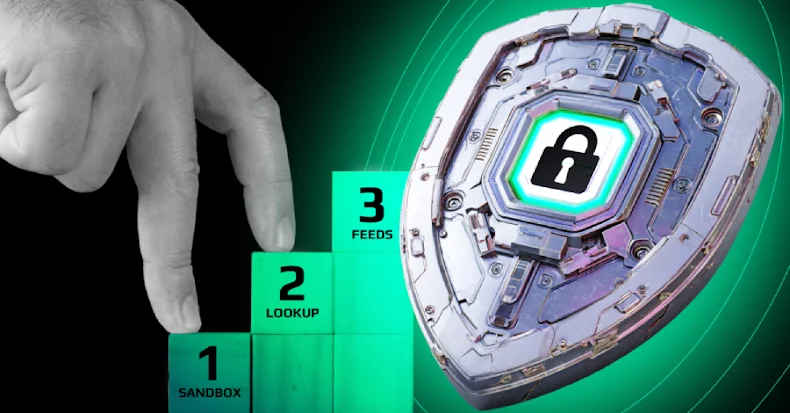
How to Close Threat Detection Gaps: Your SOC's Action Plan
-
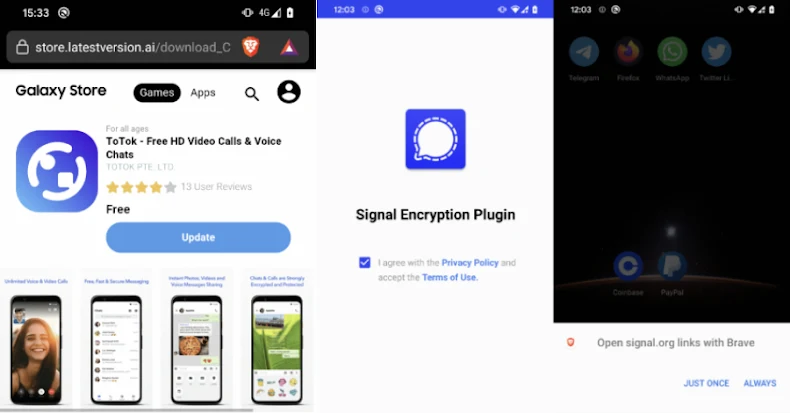
Warning: Beware of Android Spyware Disguised as Signal Encryption Plugin and ToTok Pro
-
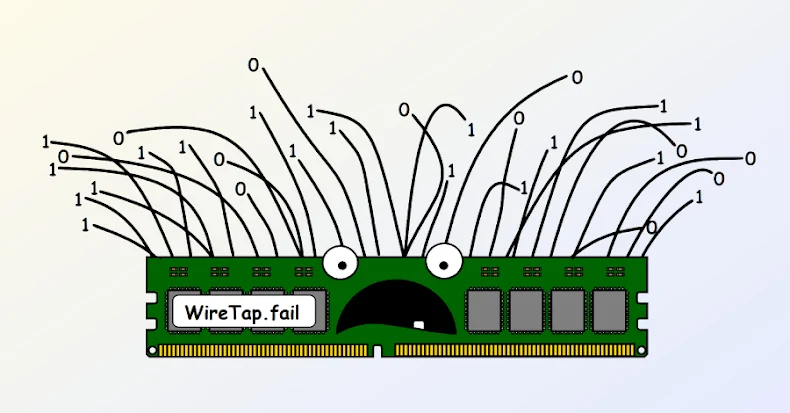
New WireTap Attack Extracts Intel SGX ECDSA Key via DDR4 Memory-Bus Interposer
-
Learn How Leading Security Teams Blend AI + Human Workflows (Free Webinar)