The Latest
-
CISO's Expert Guide To AI Supply Chain Attacks
-
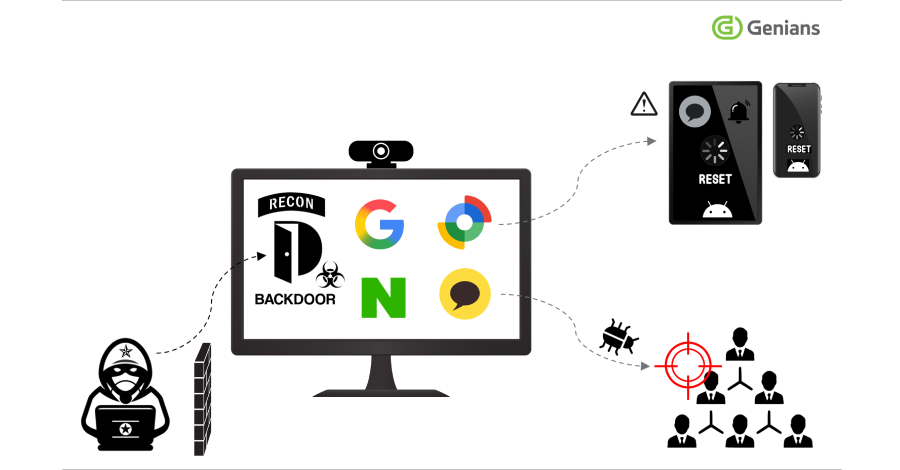
Konni Hackers Turn Google’s Find Hub into a Remote Data-Wiping Weapon
-
Hackers Exploiting Triofox Flaw to Install Remote Access Tools via Antivirus Feature
-
New Browser Security Report Reveals Emerging Threats for Enterprises