The Latest
-
ThreatsDay Bulletin: CarPlay Exploit, BYOVD Tactics, SQL C2 Attacks, iCloud Backdoor Demand & More
-
Automating Pentest Delivery: 7 Key Workflows for Maximum Impact
-
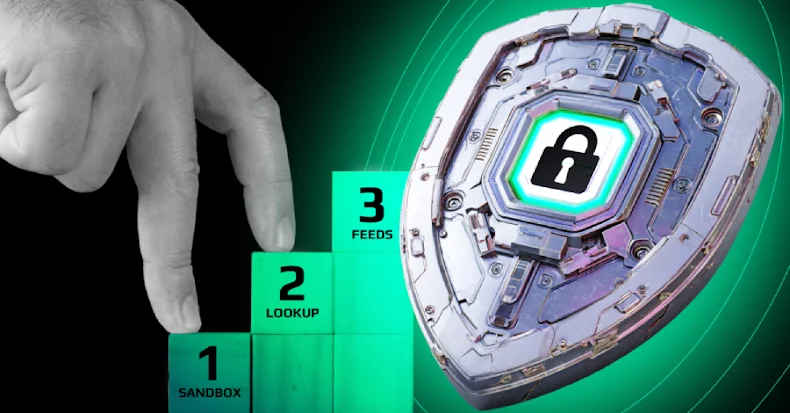
How to Close Threat Detection Gaps: Your SOC's Action Plan
-
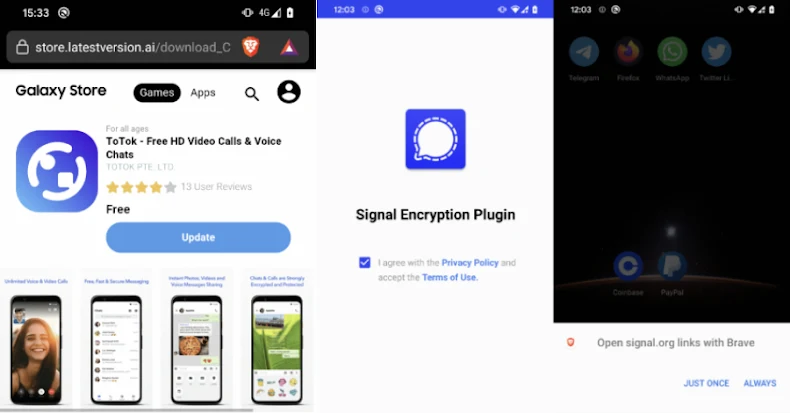
Warning: Beware of Android Spyware Disguised as Signal Encryption Plugin and ToTok Pro