The Latest
-
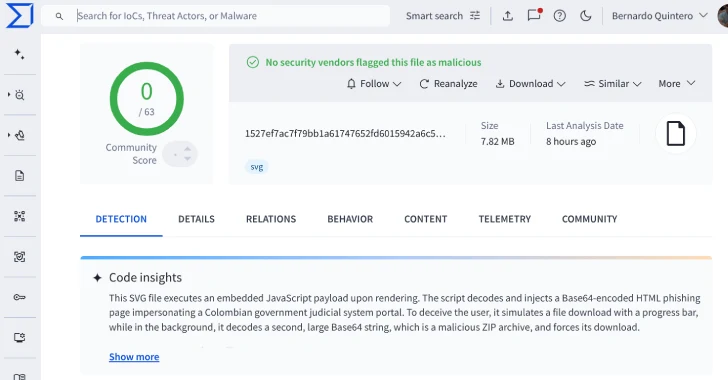
VirusTotal Finds 44 Undetected SVG Files Used to Deploy Base64-Encoded Phishing Pages
-
GhostRedirector Hacks 65 Windows Servers Using Rungan Backdoor and Gamshen IIS Module
-
Russian APT28 Deploys “NotDoor” Outlook Backdoor Against Companies in NATO Countries
-
CISA Flags TP-Link Router Flaws CVE-2023-50224 and CVE-2025-9377 as Actively Exploited