The Latest
-
2025 Cybersecurity Reality Check: Breaches Hidden, Attack Surfaces Growing, and AI Misperceptions Rising
-
Hackers Exploit Milesight Routers to Send Phishing SMS to European Users
-
New Android Banking Trojan “Klopatra” Uses Hidden VNC to Control Infected Smartphones
-
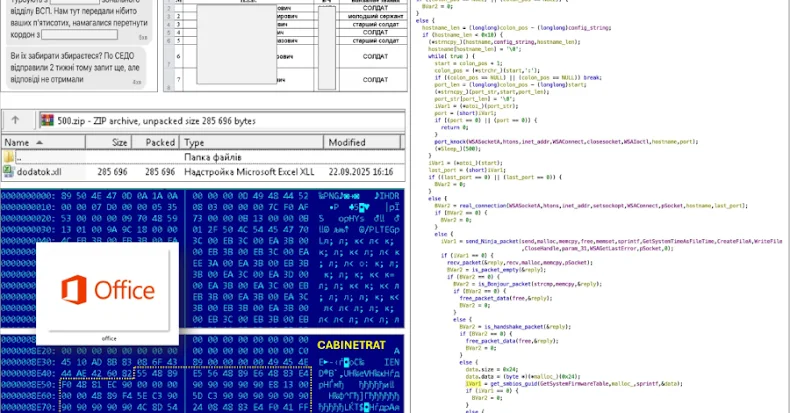
Ukraine Warns of CABINETRAT Backdoor + XLL Add-ins Spread via Signal ZIPs