The Latest
-
Hackers Hijack Blender 3D Assets to Deploy StealC V2 Data-Stealing Malware
-
3 SOC Challenges You Need to Solve Before 2026
-
CISA Warns of Active Spyware Campaigns Hijacking High-Value Signal and WhatsApp Users
-
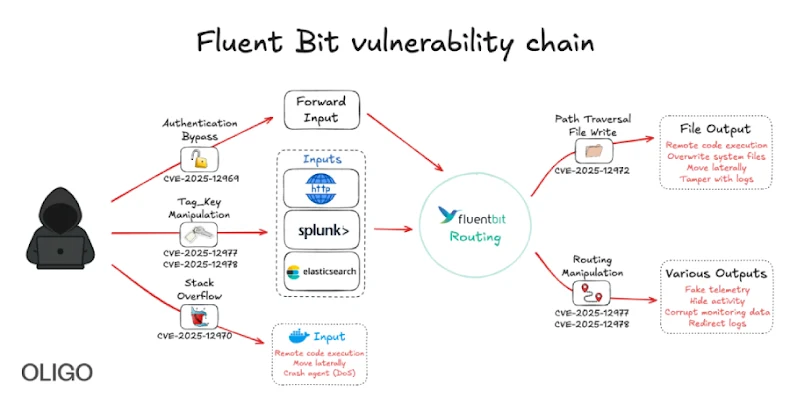
New Fluent Bit Flaws Expose Cloud to RCE and Stealthy Infrastructure Intrusions