The Latest
-
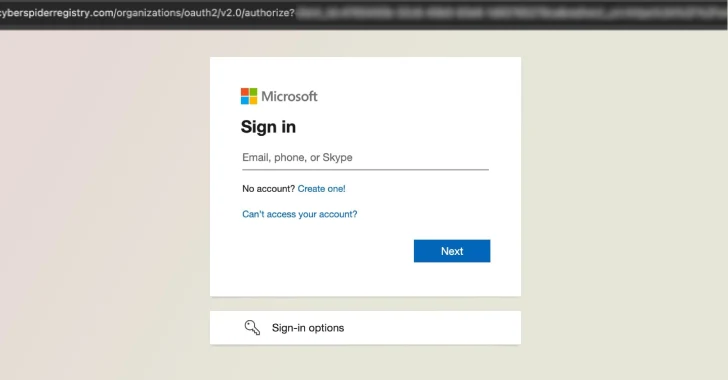
RaccoonO365 Phishing Network Shut Down After Microsoft and Cloudflare Disrupt 338 Domains
-
Self-Replicating Worm Hits 180+ npm Packages to Steal Credentials in Latest Supply Chain Attack
-
Chaos Mesh Critical GraphQL Flaws Enable RCE and Full Kubernetes Cluster Takeover
-
40+ npm Packages Compromised in Supply Chain Attack Using bundle.js to Steal Credentials