The Latest
-
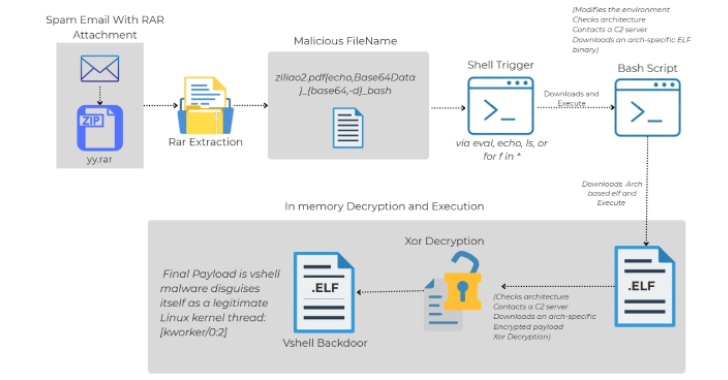
Linux Malware Delivered via Malicious RAR Filenames Evades Antivirus Detection
-
INTERPOL Arrests 1,209 Cybercriminals Across 18 African Nations in Global Crackdown
-
Chinese Hackers Murky, Genesis, and Glacial Panda Escalate Cloud and Telecom Espionage
-
Automation Is Redefining Pentest Delivery