The Latest
-
Vercel's v0 AI Tool Weaponized by Cybercriminals to Rapidly Create Fake Login Pages at Scale
-
Critical Vulnerability in Anthropic's MCP Exposes Developer Machines to Remote Exploits
-
TA829 and UNK_GreenSec Share Tactics and Infrastructure in Ongoing Malware Campaigns
-
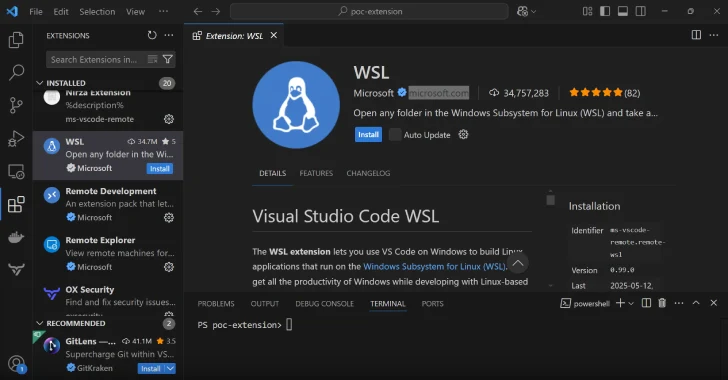
New Flaw in IDEs Like Visual Studio Code Lets Malicious Extensions Bypass Verified Status