The Latest
-
Apple Patches CVE-2025-43300 Zero-Day in iOS, iPadOS, and macOS Exploited in Targeted Attacks
-
FBI Warns FSB-Linked Hackers Exploiting Unpatched Cisco Devices for Cyber Espionage
-
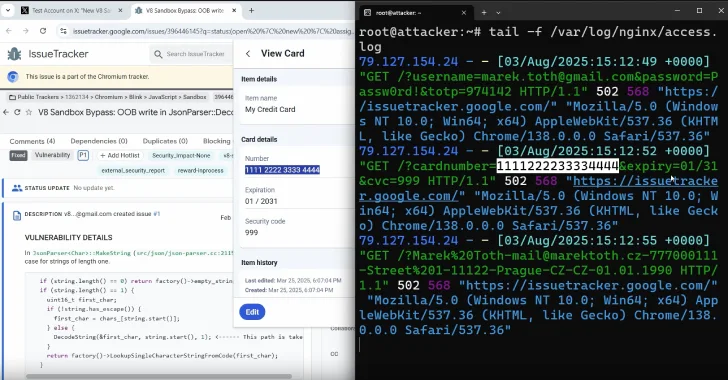
DOM-Based Extension Clickjacking Exposes Popular Password Managers to Credential and Data Theft
-
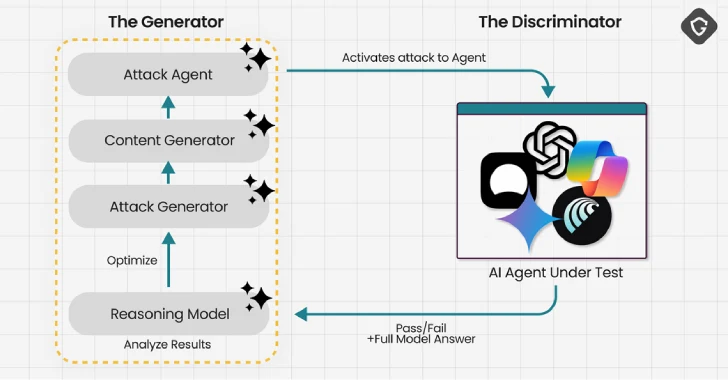
Experts Find AI Browsers Can Be Tricked by PromptFix Exploit to Run Malicious Hidden Prompts
![[Webinar] Shadow AI Agents Multiply Fast — Learn How to Detect and Control Them](https://computerodyssey.net/wp-content/uploads/2025/09/wp-header-logo-39.png)