The Latest
-
Researchers Detect Malicious npm Package Targeting GitHub-Owned Repositories
-
CISO's Expert Guide To AI Supply Chain Attacks
-
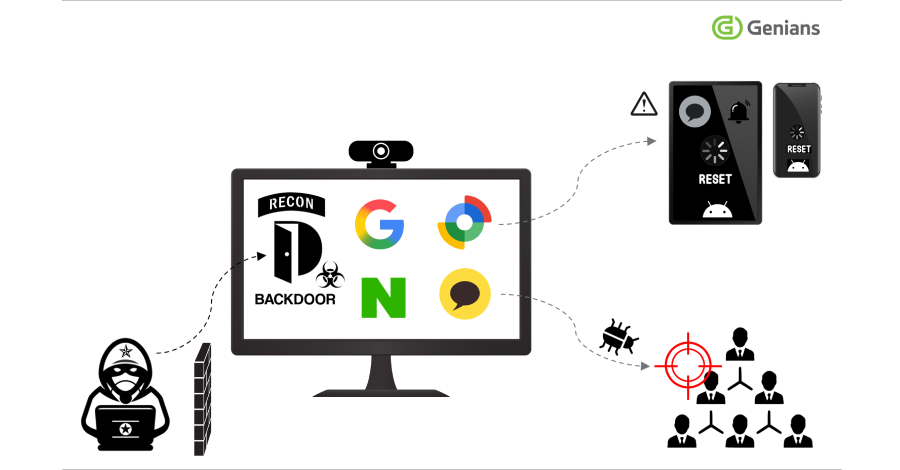
Konni Hackers Turn Google’s Find Hub into a Remote Data-Wiping Weapon
-
Hackers Exploiting Triofox Flaw to Install Remote Access Tools via Antivirus Feature