The Latest
-
⚡ Weekly Recap — SharePoint Breach, Spyware, IoT Hijacks, DPRK Fraud, Crypto Drains and More
-
Email Security Is Stuck in the Antivirus Era: Why It Needs a Modern Approach
-
Scattered Spider Hijacks VMware ESXi to Deploy Ransomware on Critical U.S. Infrastructure
-
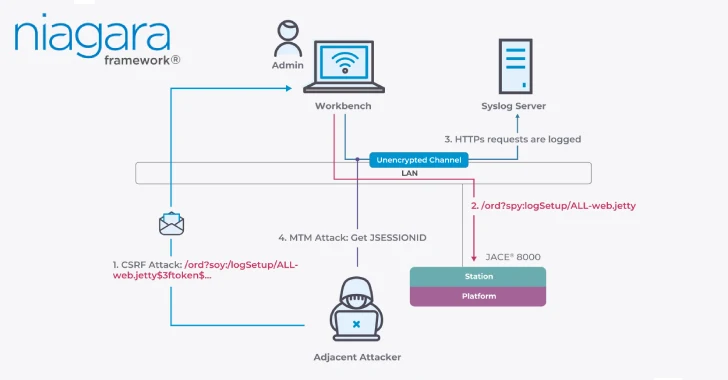
Critical Flaws in Niagara Framework Threaten Smart Buildings and Industrial Systems Worldwide