The Latest
-
XWorm 6.0 Returns with 35+ Plugins and Enhanced Data Theft Capabilities
-
New Research: AI Is Already the #1 Data Exfiltration Channel in the Enterprise
-
13-Year-Old Redis Flaw Exposed: CVSS 10.0 Vulnerability Lets Attackers Run Code Remotely
-
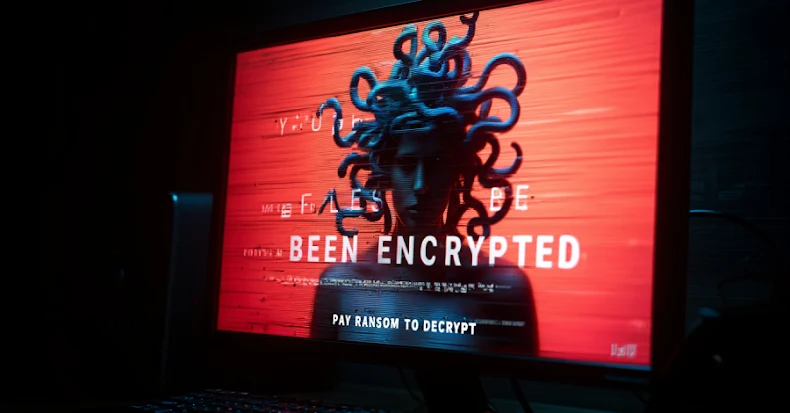
Microsoft Links Storm-1175 to GoAnywhere Exploit Deploying Medusa Ransomware