The Latest
-
Why Organizations Are Turning to RPAM
-
MS Teams Guest Access Can Remove Defender Protection When Users Join External Tenants
-
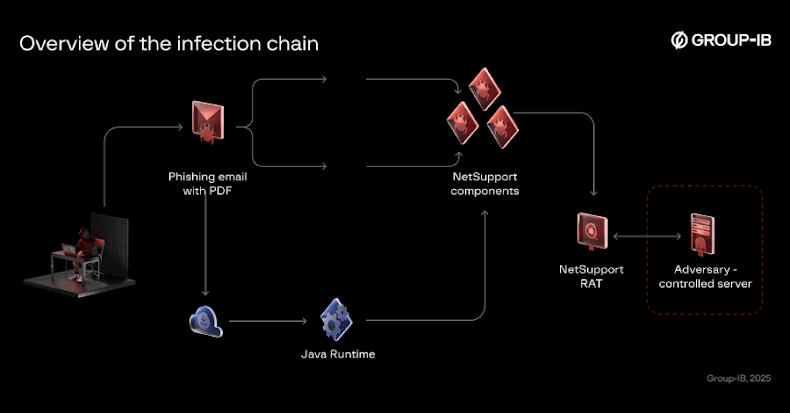
Bloody Wolf Expands Java-based NetSupport RAT Attacks in Kyrgyzstan and Uzbekistan
-
Microsoft to Block Unauthorized Scripts in Entra ID Logins with 2026 CSP Update