The Latest
-
CISA Warns of Active Exploitation of Linux Kernel Privilege Escalation Vulnerability
-
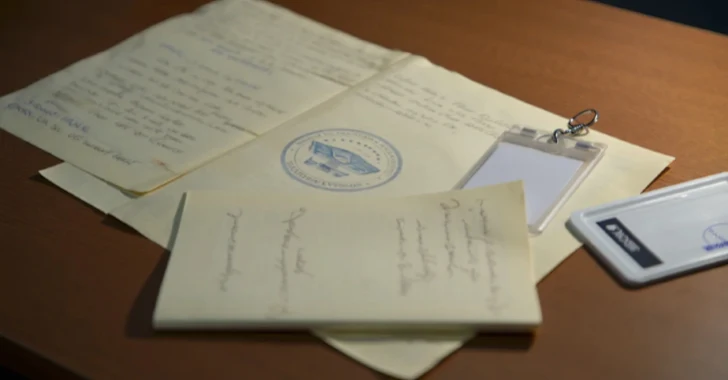
Ex-CIA Analyst Sentenced to 37 Months for Leaking Top Secret National Defense Documents
-
Iran Slows Internet to Prevent Cyber Attacks Amid Escalating Regional Conflict
-
Veeam Patches CVE-2025-23121: Critical RCE Bug Rated 9.9 CVSS in Backup & Replication