The Latest
-
Scattered Spider Hijacks VMware ESXi to Deploy Ransomware on Critical U.S. Infrastructure
-
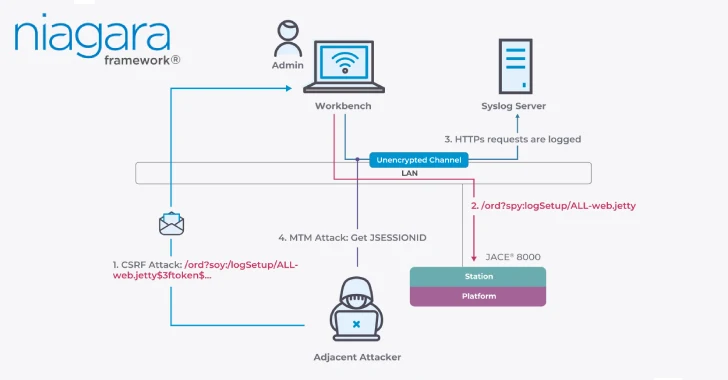
Critical Flaws in Niagara Framework Threaten Smart Buildings and Industrial Systems Worldwide
-
PoisonSeed Attack Turns Out to Be Not a FIDO Bypass After All
-
Patchwork Targets Turkish Defense Firms with Spear-Phishing Using Malicious LNK Files