The Latest
-
Deepfakes. Fake Recruiters. Cloned CFOs — Learn How to Stop AI-Driven Attacks in Real Time
-
Urgent: Google Releases Critical Chrome Update for CVE-2025-6558 Exploit Active in the Wild
-
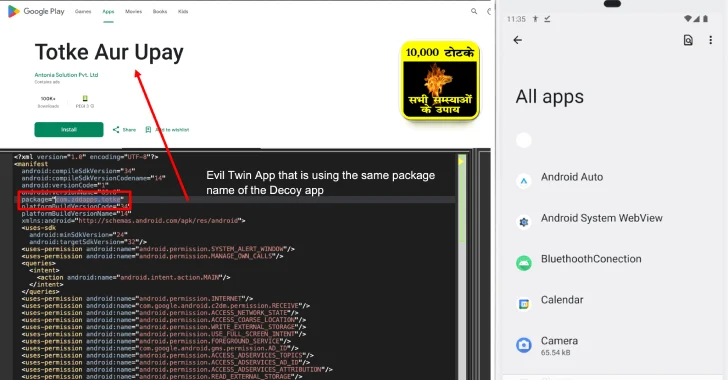
New Konfety Malware Variant Evades Detection by Manipulating APKs and Dynamic Code
-
Google AI "Big Sleep" Stops Exploitation of Critical SQLite Vulnerability Before Hackers Act