The Latest
-
U.S. Treasury Sanctions DPRK IT-Worker Scheme, Exposing $600K Crypto Transfers and $1M+ Profits
-
Someone Created the First AI-Powered Ransomware Using OpenAI's gpt-oss:20b Model
-
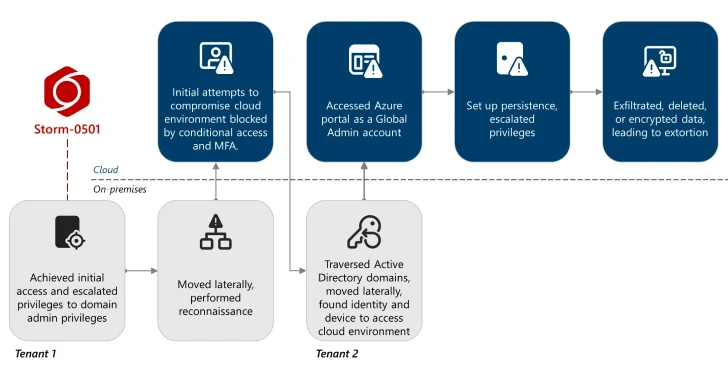
Storm-0501 Exploits Entra ID to Exfiltrate and Delete Azure Data in Hybrid Cloud Attacks
-
Someone Created First AI-Powered Ransomware Using OpenAI's gpt-oss:20b Model