The Latest
-
Automation Is Redefining Pentest Delivery
-
Ex-Developer Jailed Four Years for Sabotaging Ohio Employer with Kill-Switch Malware
-
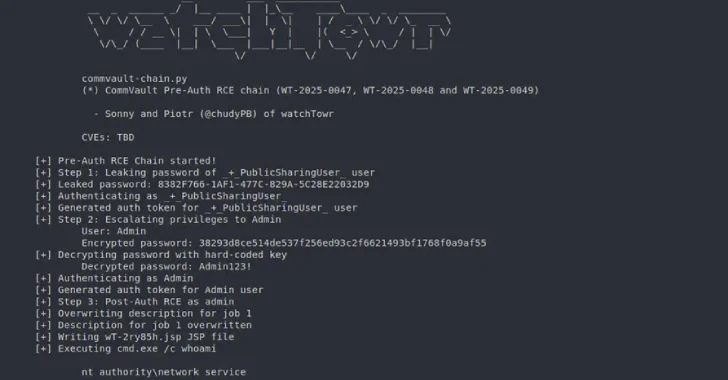
Pre-Auth Exploit Chains Found in Commvault Could Enable Remote Code Execution Attacks
-
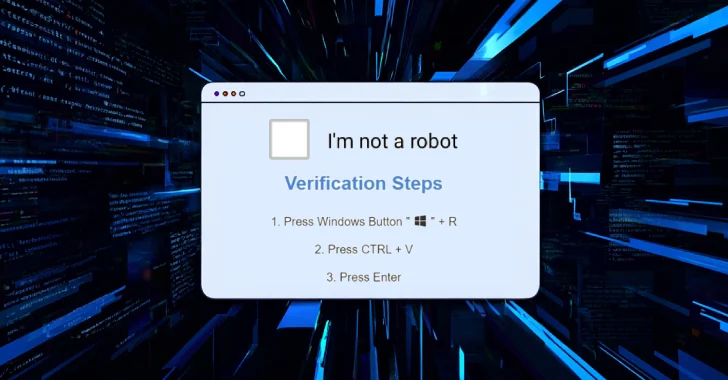
Cybercriminals Deploy CORNFLAKE.V3 Backdoor via ClickFix Tactic and Fake CAPTCHA Pages