The Latest
-
Why You Should Swap Passwords for Passphrases
-
Researchers Identify PassiveNeuron APT Using Neursite and NeuralExecutor Malware
-
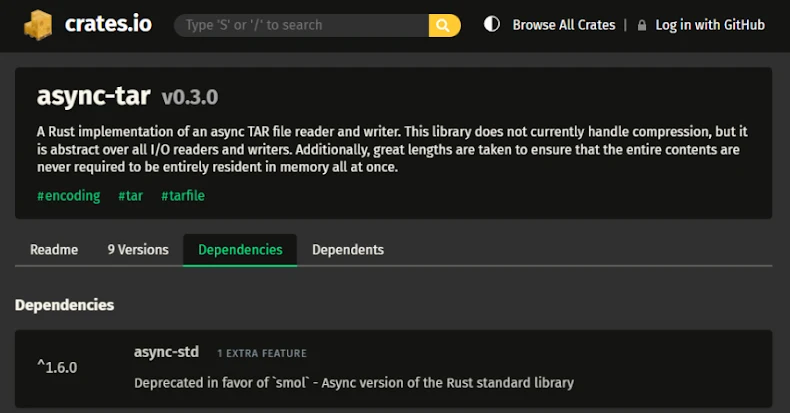
TARmageddon Flaw in Async-Tar Rust Library Could Enable Remote Code Execution
-
TP-Link Patches Four Omada Gateway Flaws, Two Allow Remote Code Execution