The Latest
-
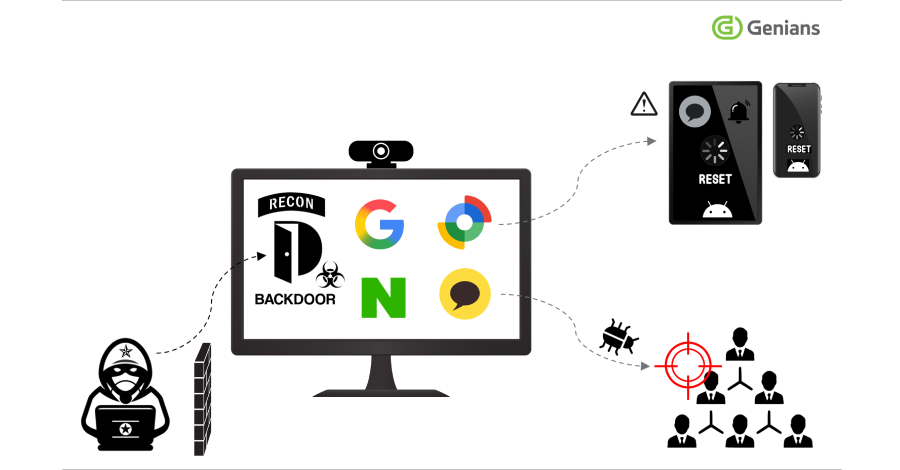
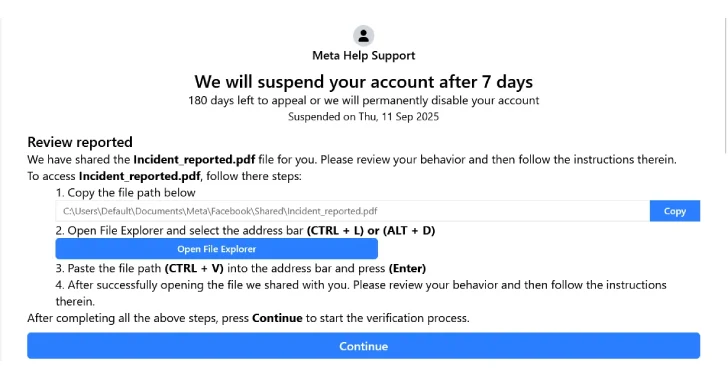
New FileFix Variant Delivers StealC Malware Through Multilingual Phishing Site
-
Securing the Agentic Era: Introducing Astrix's AI Agent Control Plane
-
Apple Backports Fix for CVE-2025-43300 Exploited in Sophisticated Spyware Attack
-
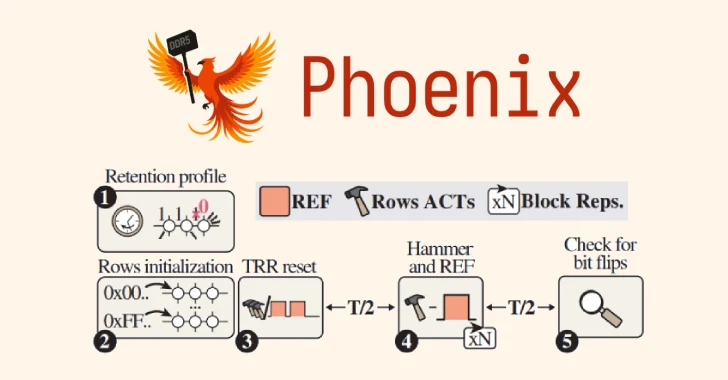
Phoenix RowHammer Attack Bypasses Advanced DDR5 Memory Protections in 109 Seconds