The Latest
-
Hackers Exploit Milesight Routers to Send Phishing SMS to European Users
-
New Android Banking Trojan “Klopatra” Uses Hidden VNC to Control Infected Smartphones
-
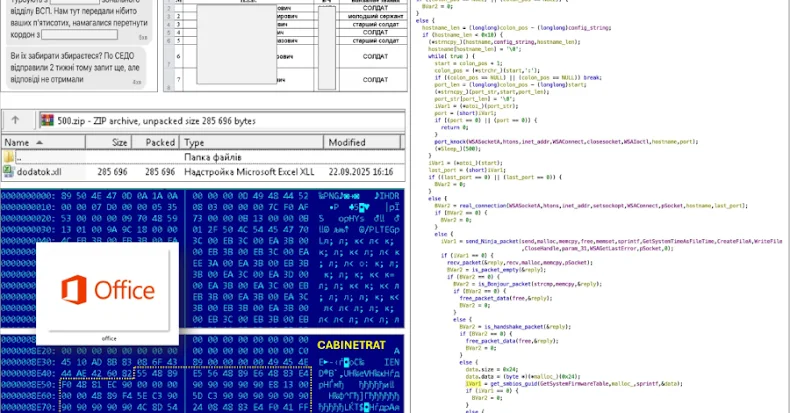
Ukraine Warns of CABINETRAT Backdoor + XLL Add-ins Spread via Signal ZIPs
-
$50 Battering RAM Attack Breaks Intel and AMD Cloud Security Protections