The Latest
-
Overcoming Risks from Chinese GenAI Tool Usage
-
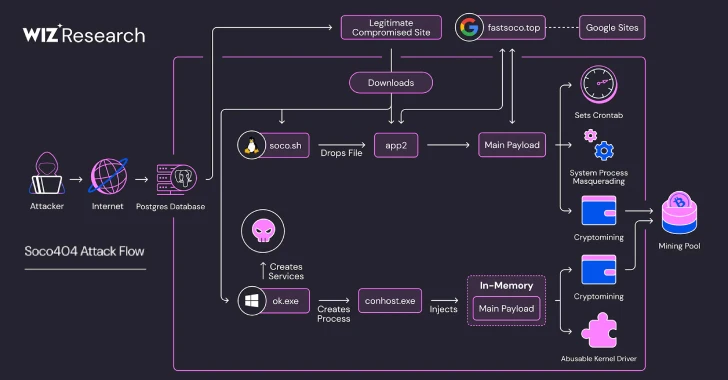
Soco404 and Koske Malware Target Cloud Services with Cross-Platform Cryptomining Attacks
-
Fire Ant Exploits VMware Flaws to Compromise ESXi Hosts and vCenter Environments
-
Critical Mitel Flaw Lets Hackers Bypass Login, Gain Full Access to MiVoice MX-ONE Systems