The Latest
-
NHS Warns of PoC Exploit for 7-Zip Symbolic Link–Based RCE Vulnerability
-
Salesforce Flags Unauthorized Data Access via Gainsight-Linked OAuth Activity
-
Tsundere Botnet Expands Using Game Lures and Ethereum-Based C2 on Windows
-
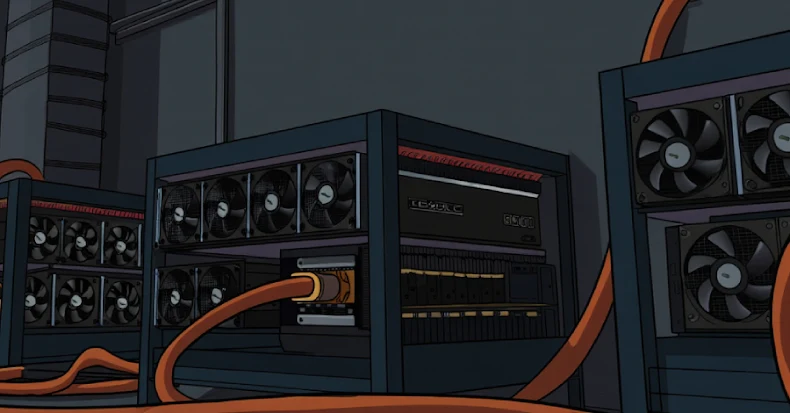
ShadowRay 2.0 Exploits Unpatched Ray Flaw to Build Self-Spreading GPU Cryptomining Botnet