The Latest
-
U.S. Secret Service Seizes 300 SIM Servers, 100K Cards Threatening U.S. Officials Near UN
-
SolarWinds Releases Hotfix for Critical CVE-2025-26399 Remote Code Execution Flaw
-
ShadowV2 Botnet Exploits Misconfigured AWS Docker Containers for DDoS-for-Hire Service
-
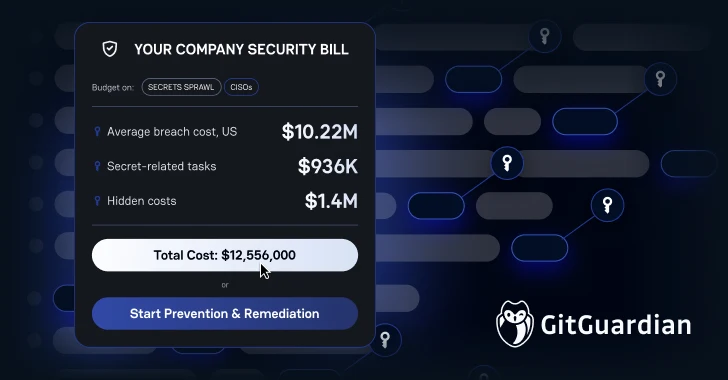
Lean Teams, Higher Stakes: Why CISOs Must Rethink Incident Remediation